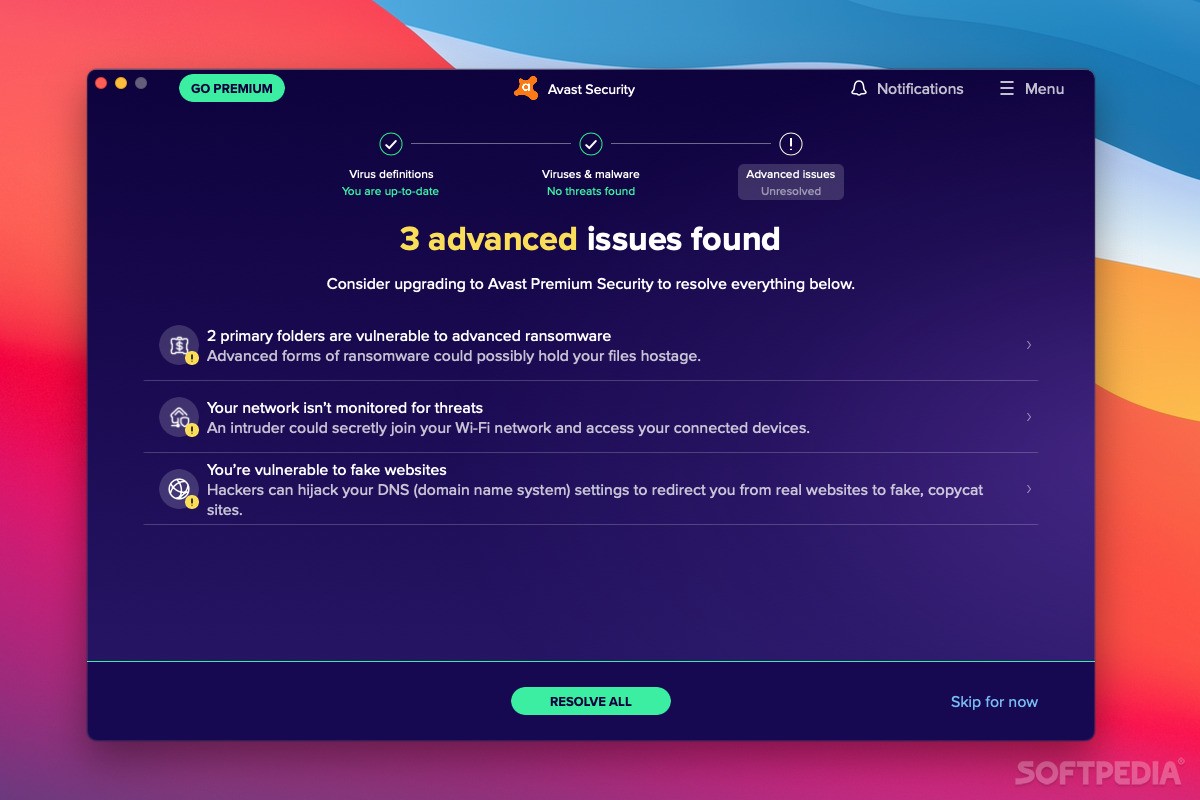
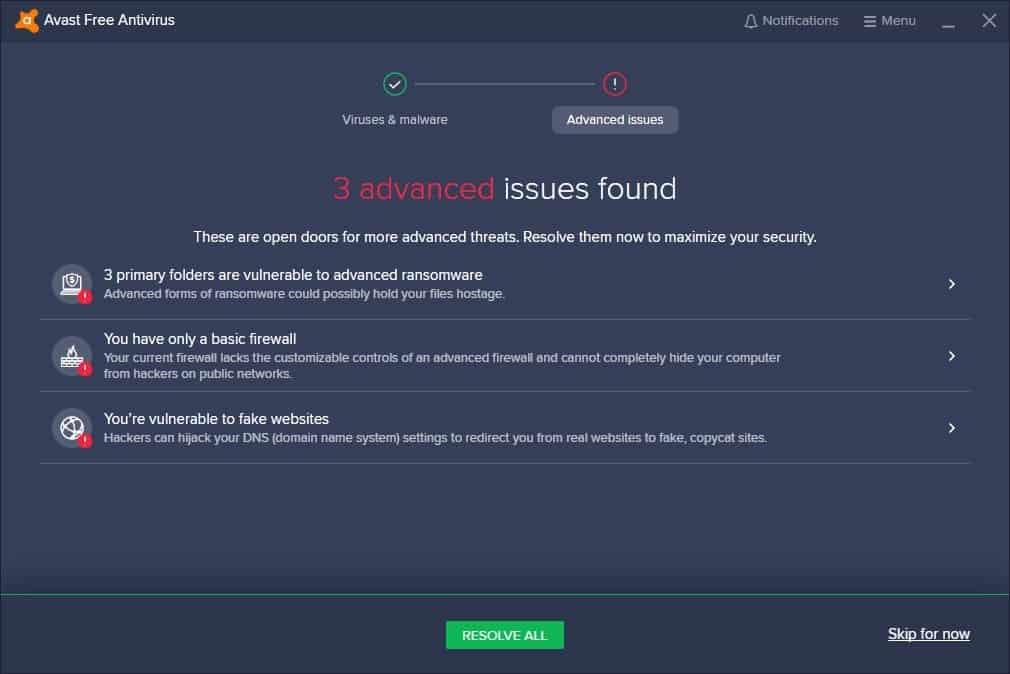
Solved] Complete Exercise 9.3, 'Using Avast! Antivirus,' from the Summary section of Ch. 9, 'Defending Against Virus Attacks,' of Network Defense an... | Course Hero

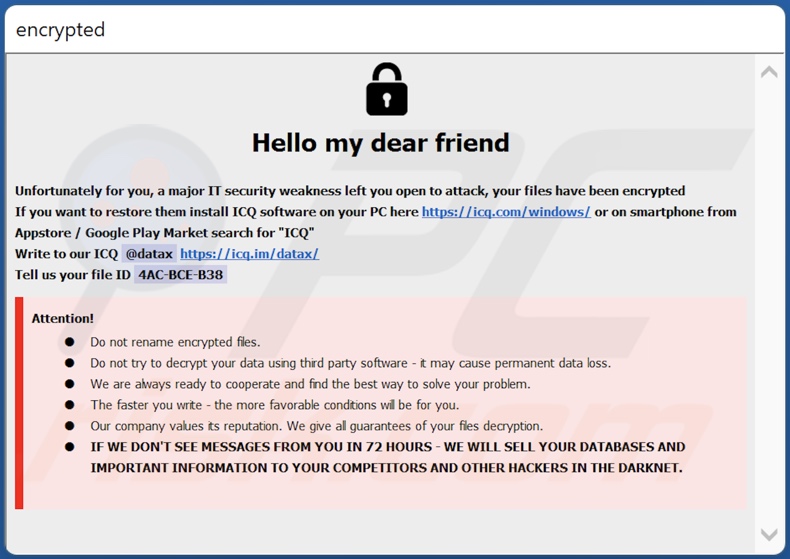
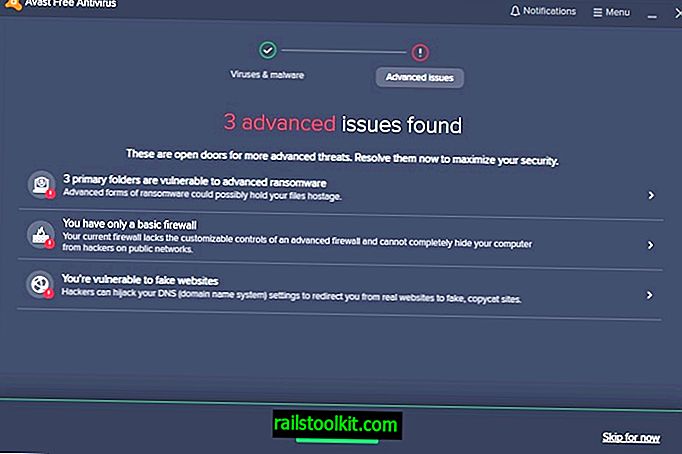
Stopping ransomware where it counts: Protecting your data with Controlled folder access - Microsoft Security Blog












![Avast Antivirus Review 2022 [Updated] - Online Help Guide Avast Antivirus Review 2022 [Updated] - Online Help Guide](https://onlinehelpguide.com/wp-content/uploads/2020/03/McAfee-Antivirus-Review.jpg?ezimgfmt=rs:368x184/rscb2/ng:webp/ngcb2)
![Avast Antivirus Review 2022 [Updated] - Online Help Guide Avast Antivirus Review 2022 [Updated] - Online Help Guide](https://onlinehelpguide.com/wp-content/uploads/2020/03/Avast-Antivirus-Review-2020.jpg)